
Almost two dozen apps with more than 2 million downloads have been removed from the Google Play market after researchers found they contained a device-draining backdoor that allowed them to surreptitiously download files from an attacker-controlled server.
The 22 rogue titles included Sparkle Flashlight, a flashlight app that had been downloaded more than 1 million times since it entered Google Play sometime in 2016 or 2017, antivirus provider Sophos said in a blog post published Thursday. Beginning around March of this year, Sparkle Flashlight and two other apps were updated to add the secret downloader. The remaining 19 apps became available after June and contained the downloader from the start.
“Serious harm”
By the time Google removed the apps in late November, they were being used to click endlessly on fraudulent ads. “Andr/Clickr-ad,” as Sophos has dubbed the family of apps, automatically started and ran even after a user force-closed them, functions that caused the apps to consume huge amounts of bandwidth and drain batteries. In Thursday’s post, Sophos researcher Chen Yu wrote:
Andr/Clickr-ad is a well-organized, persistent malware that has the potential to cause serious harm to end users, as well as the entire Android ecosystem. These apps generate fraudulent requests that cost ad networks significant revenue as a result of the fake clicks.
From the user’s perspective, these apps drain their phone’s battery and may cause data overages as the apps are constantly running and communicating with servers in the background. Furthermore, the devices are fully controlled by the C2 server and can potentially install any malicious modules upon the instructions of the server.
The apps worked by reporting to an attacker-controlled domain, mobbt.com, where the infected phones would download ad-fraud modules and receive specific commands every 80 seconds. The modules caused the phones to click on huge numbers of links that hosted fraudulent apps. To prevent users from suspecting their phones were infected, the apps displayed the ads in a window that was zero pixels high and zero wide.
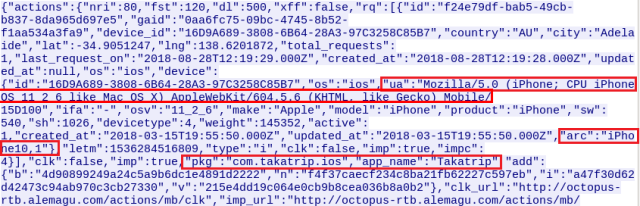
To give defrauded advertisers the false impression the clicks were coming from a much larger pool of authentic users, Andr/Clickr-ad manipulated user-agent strings to pose as a wide variety of apps running on a wide variety of phones, including iPhones. The following image shows a malicious app running on an Android virtual device identifying itself as running on an iPhone.
Many of the malicious Google Play apps were made by developers who had titles in the iOS App Store.
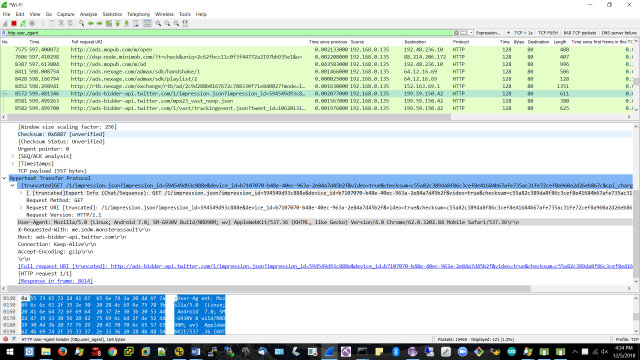
The captured traffic displayed below, also taken from an Android virtual device, shows Andr/Clickr-ad abusing Twitter’s ad network by posing as an ad running on a Samsung Galaxy S7:
Maximizing profits, spreading out the fraud
In all, Sophos observed server data causing the fraudulent clicks to appear as if they were coming from Apple models ranging from the iPhone 5 to 8 Plus and from 249 different forged models from 33 distinct brands of Android phones (purportedly) running Android OS versions ranging from 4.4.2 to 7.x. The false user-agent data likely served several purposes. First, the iPhone labels may have allowed the scammers to fetch higher prices, since some advertisers will pay premiums when their ads are viewed by iPhone users. Second (and more importantly), the false labeling gave the impression the ads were being clicked on by a much larger number of devices.
To ensure maximum profit, Andr/Clickr-ad apps were programmed to run automatically each time an infected phone was rebooted, by using a BOOT_COMPLETED broadcast. In the event a user force-closed an app, developers created a sync adapter to restart the app three minutes later. The apps checked for new ad commands as often as every 80 seconds and checked for new module downloads as often as every 10 minutes.
Thursday’s post is the latest evidence that Google can’t proactively police its own market for apps that pose a serious security threat, though in fairness the company is very quick to remove titles once they’re reported. While Google removed the malicious apps on November 25, it’s not clear that all phones that downloaded them have been disinfected. Google representatives didn’t respond to an email asking about this. Android has the ability to automatically remove apps that are later found to be abusive, but it’s worth manually checking.
The 22 apps listed by Sophos are:
| Package Name | Title | Sha1 |
| com.sparkle.flashlight | Sparkle FlashLight | 9ed2b260704fbae83c02f9f19a2c4e85b93082e7 |
| com.mobilebt.snakefight | Snake Attack | 0dcbbae5d18c33039db726afd18df59a77761c03 |
| com.mobilebt.mathsolver | Math Solver | be300a317264da8f3464314e8fdf08520e49a55b |
| com.mobilebt.shapesorter | ShapeSorter | e28658e744b2987d31f26b2dd2554d7a639ca26d |
| com.takatrip.android | Tak A Trip | 0bcd55faae22deb60dd8bd78257f724bd1f2fc89 |
| com.magnifeye.android | Magnifeye | 7d80bd323e2a15233a1ac967bd2ce89ef55d3855 |
| com.pesrepi.joinup | Join Up | c99d4eaeebac26e46634fcdfa0cb371a0ae46a1a |
| com.pesrepi.zombiekiller | Zombie Killer | 19532b1172627c2f6f5398cf4061cca09c760dd9 |
| com.pesrepi.spacerocket | Space Rocket | 917ab70fffe133063ebef0894b3f0aa7f1a9b1b0 |
| com.pesrepi.neonpong | Neon Pong | d25fb7392fab90013e80cca7148c9b4540c0ca1d |
| app.mobile.justflashlight | Just Flashlight | 6fbc546b47c79ace9f042ef9838c88ce7f9871f6 |
| com.mobile.tablesoccer | Table Soccer | fea59796bbb17141947be9edc93b8d98ae789f81 |
| com.mobile.cliffdiver | Cliff Diver | 4b23f37d138f57dc3a4c746060e57c305ef81ff6 |
| com.mobile.boxstack | Box Stack | c64ecc468ff0a2677bf40bf25028601bef8395fc |
| net.kanmobi.jellyslice | Jelly Slice | 692b31f1cd7562d31ebd23bf78aa0465c882711d |
| com.maragona.akblackjack | AK Blackjack | 91663fcaa745b925e360dad766e50d1cc0f4f52c |
| com.maragona.colortiles | Color Tiles | 21423ec6921ae643347df5f32a239b25da7dab1b |
| com.beacon.animalmatch | Animal Match | 403c0fea7d6fcd0e28704fccf5f19220a676bf6c |
| com.beacon.roulettemania | Roulette Mania | 8ad739a454a9f5cf02cc4fb311c2479036c36d0a |
| com.atry.hexafall | HexaFall | 751b515f8f01d4097cb3c24f686a6562a250898a |
| com.atry.hexablocks | HexaBlocks | ef94a62405372edd48993030c7f256f27ab1fa49 |
| com.atry.pairzap | PairZap | 6bf67058946b74dade75f22f0032b7699ee75b9e |
Android users should be highly selective about the apps they install. Carefully reading reviews can sometimes help, but the rave reviews many of the Andr/Clickr-ad apps received underscores the limits to this measure. Ultimately, the advice that makes the most sense is to install as few apps as possible, particularly if, as is the case with flashlight apps, the same function is offered inside the Android OS itself.
Be the first to comment